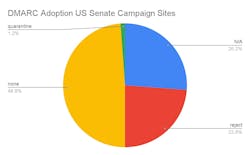
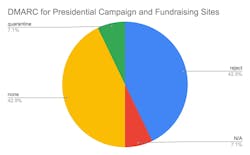
Securing political campaigns from cyber threats has never been more urgent. It is critical to secure communications that handle sensitive exchanges with voters, contributors, donations and coordinate complex operations. Campaigns make exceptionally rich targets for cyber espionage and exploitation, with our open-source research, demonstrating nearly 75% of US Senate campaign websites having not achieved Domain-based Message Authentication, Reporting & Conformance (DMARC) compliance. Their reliance on sensitive information, such as strategic plans, voter demographic data, and donor communications offer tantalizing prospects for influence, disruption, or other operations designed to undermine trust in fair elections.
In the United States, many campaign websites and digital infrastructures lack robust cybersecurity measures. Despite the importance of email security, Red Sift’s analysis shows that a troubling majority of U.S Senate and Presidential political campaign websites lack DMARC protections. Without properly managed DMARC, these campaigns are vulnerable to phishing and spoofing attempts, which can lead to breaches, leaking, and other significant security breaches. For campaigns, time pressures amplify these risks, allowing attackers to exploit lapses in security at critical moments.
Influence operations, cyber hygiene, and public trust
Historically, Russian attacks against U.S. campaigns have focused on influence operations, hoping to alter outcomes in their favor. More recently, Iran has become a formidable cyber attacker, presently focusing more on disrupting election processes than swaying voters. Russian, Chinese, and Iranian state actors have repeatedly sought to take advantage of weak email security and cyber hygiene, often to great effect as in the cases of the 2015-2016 Russian GRU hacks and most recently Iranian “hack and leak” attempts against current and former U.S. officials.
Personal email accounts are not exempt from attack either: Russia’s cyber attacks against the private email accounts of the former chair of Hillary Clinton’s presidential campaign John Podesta and former Secretary of State Hillary Clinton were orchestrated by Russian intelligence and ultimately published on Wikileaks.
Although their objectives may differ, the TTPs for malign actors looking to undermine elections are markedly similar: low level DDOS attacks and infostealers remain common as do phishing and social engineering attacks aimed at email communications. Acutely, campaigns should have robust technical and policy measures in place to mitigate the rise in spearphishing, impersonation, and domain-spoofing attacks.
Today, campaign domain sites and associated email accounts remain prime vectors for exploits such as spoofed domains. As noted in FBI and CISA advisories, DMARC policies play a crucial role in preventing email spoofing and phishing attacks by ensuring that emails sent from a domain are authenticated. Properly configured, these measures would help protect a political campaign’s reputation, ultimately helping campaign operations while safeguarding against cyberattacks that can undermine the democratic process.
While there is no silver bullet for email cybersecurity, properly configured and managed DMARC is crucial for political campaigns as it helps protect against email spoofing, ensuring that only legitimate communications are sent from the campaign’s domain. This is vital for maintaining trust with voters and donors, as it prevents phishing attacks that could compromise sensitive information or spread disinformation. Ultimately, by securing email communications, DMARC safeguards the campaign’s reputation, helping to prevent attackers from tarnishing the brand with fake emails.
As last month’s joint CISA/FBI public service announcement describes, adversaries seek to undermine faith in U.S. elections by targeting several key areas: spreading disinformation, leaking or manipulating sensitive information to create misleading narratives, swaying public opinion, and discrediting candidates. Additionally, hacktivists and foreign powers may seek to access confidential strategic plans, gaining insights into a campaign’s tactics or leaking this information to sway opinion.
Cyber-attacks can also disrupt campaign operations, potentially slowing momentum. Taken together, these efforts ultimately aim to undermine public trust in the electoral process, destabilizing the political landscape, and potentially aligning election outcomes with the interests of other states.
With heightened concerns around election integrity, implementing DMARC demonstrates a campaign’s commitment to secure, authentic communication and adherence to cybersecurity standards. This not only builds voter trust but also contributes to the overall security of the political process and the integrity of democratic processes. Campaigns are known targets of states and state-sponsored cybercriminals, as such prioritizing robust cybersecurity measures, particularly DMARC implementation, is essential to safeguarding both political campaigns and preserving public trust.
Note: This blog is courtesy of Red Sift and Dr. Sean Costigan. You can see his original blog and other articles here.