RAD Security unveils AI incident investigation for behavioral detection and response
As RAD Security takes the stage as a finalist in the Black Hat Startup Spotlight Competition, it unveils the first-ever AI-powered incident investigation capability for behavioral detection and response. Today, cloud security is based almost exclusively on signature-based detections, which are notorious for burdening security teams with false positives. RAD Security combines AI-powered incident investigation with behavioral, signature-less detections, to significantly reduce false positives and provide much-needed relief for overburdened security teams.
“By definition, signatures are stateless, making investigations based on the signature-focused approach inaccurate and tedious,” says CTO and Co-Founder Jimmy Mesta. “By adding AI-powered investigations to behavioral detection, which is already a step ahead of signature-based detection in accuracy, security teams can quickly get light years ahead in the accurate assessment of incidents.”
RAD’s behavioral approach and AI-powered investigations result in the lowering of false positives on their own; but by putting these two capabilities together, RAD enables security teams to achieve a multiplier effect. The enhanced accuracy of behavioral methods versus signature-based methods is easily demonstrated using multiple examples of attack tactics like reverse shells, access to sensitive data, and a Sudo CVE.
In these examples, while signatures can be easily bypassed by avoiding the exact parameters, they are detected by RAD’s behavioral solution. By the same token, a behavioral drift event is not always a malicious event, so the addition of the AI investigation capability ensures additional accuracy. AI is particularly suited for looking across large sets of data and quick contextualization, making it a natural investigation tool and engine to analyze benign versus malicious drift.
Throughout the history of cyber security, and most famously in the endpoint and network security markets, signatures have eventually been replaced by behavioral methods in response to an evolving threat landscape. Today, the cloud security category is nearly entirely composed of signature-based approaches with runtime security and Cloud Workload Protection (CWPP) that are standalone or part of a broader Cloud Native Application Protection Platform (CNAPP). In sharp contrast to signature-based CNAPPs, or posture-focused Cloud Security Posture Management (CSPM), RAD Security’s Cloud Detection and Response (CDR) solution creates behavioral baselines of unique good behavior to detect zero day attacks, enriching detections with real-time identity and infrastructure context that inform response actions.
More and more, detection and response is being accomplished by fewer and fewer dedicated people, with 22% of security professionals reporting recent layoffs at their company. The workforce reductions are an even more acute pain in cloud security, with 65% of cybersecurity and infosecurity professionals claiming burnout due to skill gaps. Even though a full 95% of IT decision makers feel their team has been negatively impacted by the cloud security skills gap, cloud native adoption continues, and analysts predict that, by 2025, 95% of new applications will be built using cloud native workloads.
Zero days like the XZ Backdoor are now a regular occurrence, making detection and response in cloud native environments more important than ever.
RAD Security has introduced multiple new features to help security teams adopt new innovation that will help them address these alarming trends and emerging threats:
- Amazon EKS Add-on: RAD Security is now available as an Amazon EKS Add-on in the AWS Marketplace for Containers. This means customers can now provision the real-time KSPM and runtime features of the RAD platform directly from EKS, for real-time visibility into their Kubernetes risk as well as signatureless cloud detection and response.
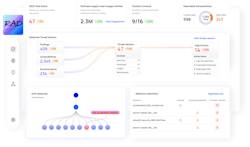
- Automated AI-Powered Investigation: RAD Security uses LLMs to quickly analyze multiple behavioral detections and determine whether an incident is malicious or benign, including real-time infrastructure and identity context.
- Findings Center: All incidents are now available in an easy to navigate console, making detection and investigation easier and quicker.
- RAD Open Source Catalog: New version details and new open source images have now been added to the RAD Catalog, detailing the changes in behavioral fingerprints over time and bolstering the behavioral workload fingerprint standard.
Schedule a meeting with the RAD Security team at the Black Hat Conference this week to discuss improving detection accuracy for attacks in your cloud environments. The team will be exhibiting at booth #219 in Startup City, and at 4:45PM EST they will be presenting at the Innovators and Investors Summit as one of the four finalists in the Startup Spotlight competition.